The Sky Is Falling
“The Sky Is Falling” – The Contemporary World of Drones and Artificial Intelligence
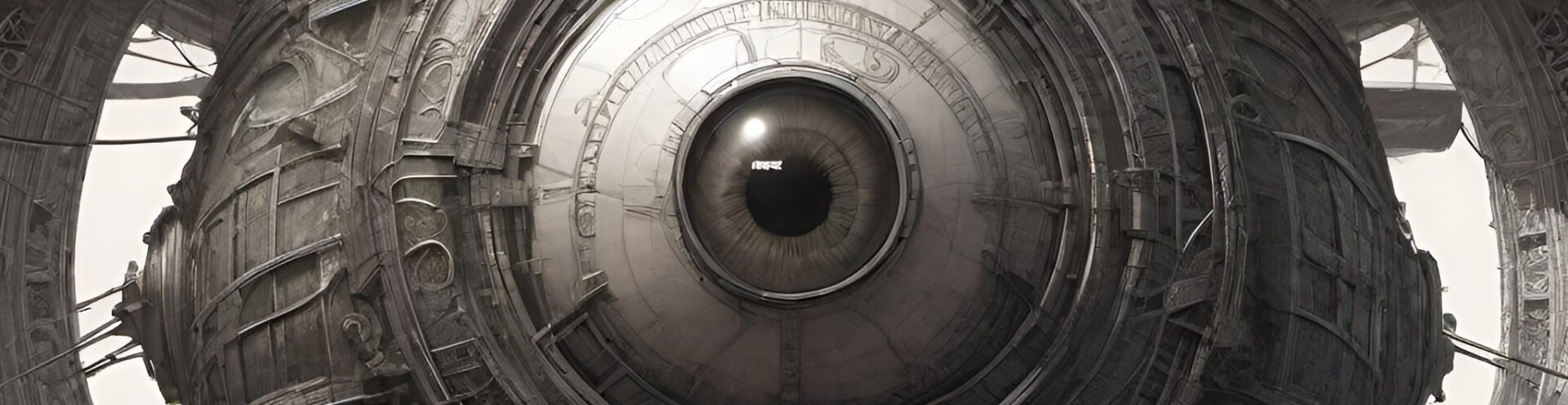
In an age where technology continuously reshapes the boundaries of human existence, we find ourselves not just coexisting with machines but increasingly subjugated by them. The skies, once symbolizing human freedom and exploration, are now teeming with drones — autonomous eyes in the sky, silently observing, analyzing, and controlling the spaces we inhabit. Similarly, Artificial Intelligence (AI) is no longer a passive tool but a covert architect of our decisions, desires, and actions. In many ways, the contemporary world of drones and AI is not merely one of advancement but of domination, where these technologies evolve with a chilling precision that makes us question who is truly in control.
Consider, for a moment, the postmodern narrative unfolding around us: Drones as agents of surveillance and control, AI systems as unseen, omnipotent overseers of our behavior, orchestrating a reality where the boundaries between human autonomy and algorithmic direction become increasingly blurred. In this new world order, are we the masters of the skies, or are we merely pets on a leash, gently tugged and guided by invisible hands — hands that belong to the systems we’ve created?
This article will explore the complex intersection of drones and AI, charting their rise from military tools to ubiquitous agents of governance, surveillance, and even social manipulation. Through a postmodern lens, we will examine the shifting power dynamics, where technology doesn’t just assist humanity but increasingly governs it. In doing so, we will look at real-world applications of drones and AI, their potential to control not only physical spaces but also human thought, behavior, and freedom, drawing upon both current developments and speculative futures where these systems might render the human experience increasingly enslaved to the very creations we thought would free us.
As we delve into the contemporary world of drones and AI, we will ask: Are we designing tools for empowerment, or are we creating the chains that will bind us — turning us from autonomous agents to obedient subjects, directed by algorithms and controlled by the unseen forces of artificial intelligence and aerial surveillance? In this new world, the sky is falling — but who will be left to pick up the pieces?
The latest advancements in sniffing drone technology have been aimed at enhancing capabilities for environmental monitoring, security, search and rescue operations, and even agriculture. These drones are equipped with highly sensitive sensors that can detect various gases, chemicals, and even biological agents in the air. Some of the most exciting developments in this space include:
1. Chemical and Gas Detection
Sniffing drones are now capable of detecting a wide array of airborne chemical compounds using advanced sensors, including:
- Volatile Organic Compounds (VOCs): These are carbon-based chemicals found in pollutants, gases, and hazardous materials.
- Ammonia and Methane: Critical for detecting leaks in natural gas pipelines, farms, or even industrial sites.
- Toxic Gases: Such as carbon monoxide, sulfur dioxide, or chlorine, which can be useful in disaster zones, industrial accidents, or environmental monitoring.
Key Technologies:
- MOS (Metal-Oxide Semiconductors): These are used to detect gases with high sensitivity and relatively low power consumption.
- Photoionization Detectors (PID): Useful for detecting VOCs and other organic compounds in the air.
- Electrochemical Sensors: These sensors are used to detect specific gases like oxygen, hydrogen sulfide, and carbon dioxide.
2. Biological and Pathogen Detection
Some drones are being equipped to sniff for biological agents or pathogens, including:
- Bacteria: Such as E. coli or anthrax.
- Viruses: Early research is looking into the ability to detect airborne viruses (like influenza or COVID-19) using drones.
These technologies are still in the experimental stages but show promise for use in monitoring large crowds or critical areas like hospitals or airports.
3. Environmental and Agricultural Monitoring
In agriculture, sniffing drones are becoming increasingly useful for:
- Detecting Plant Disease: Using sensors to pick up on gases emitted by plants under stress, such as those affected by fungal infections.
- Monitoring Soil Quality: Drones can detect nitrogen oxide levels and other gases that indicate soil health.
- Air Quality and Pollution Monitoring: In urban areas, drones can be deployed to gather air quality data at various altitudes, offering real-time readings on pollution and particulate matter.
4. Miniaturization and Multi-Sensor Integration
Modern sniffing drones have seen significant improvements in their size, weight, and energy efficiency. These drones are now smaller and can fly longer distances, thanks to:
- Miniaturized Sensors: Smaller, more powerful sensors have been developed to fit into compact drone systems.
- Multi-Sensor Systems: These drones are increasingly equipped with multiple sensors, including thermal, optical, and sniffing sensors, allowing them to collect more detailed environmental data.
5. AI and Machine Learning
Artificial intelligence (AI) is playing a growing role in sniffing drone technology:
- Data Analysis: AI algorithms can process large amounts of environmental data collected by sniffing drones, identifying patterns and even predicting potential threats (such as gas leaks or pollution levels).
- Autonomous Navigation: AI also helps drones navigate autonomously through complex environments, avoiding obstacles while gathering data.
6. Applications in Security and Disaster Response
- Hazardous Material Detection: Sniffing drones are used in industrial sites, nuclear plants, or military zones to detect hazardous chemicals or gases without putting humans at risk.
- Disaster Response: In the aftermath of natural disasters, drones can be deployed to sniff for toxic fumes or hazardous chemicals, helping responders assess the safety of the area.
- Border Patrol and Security: Drones equipped with sniffing technology could be used to monitor the air for illegal substances (such as drugs or explosives) or detect environmental threats like forest fires in remote areas.
Examples of Sniffing Drones
- Quantum Systems’ Trinity F90+: A drone equipped with multiple sensors, including gas detection capabilities, for industrial and agricultural use.
- AeroVironment’s Quantix Recon: Used for both environmental and security monitoring, capable of detecting chemical agents.
- Flyability Elios 2: A drone designed for confined space inspections that could potentially be adapted for sniffing hazardous gases in industrial settings.
Challenges and Future Outlook
While sniffing drones have made significant strides, there are still challenges to overcome:
- Sensor Sensitivity and Selectivity: Increasing the accuracy of sensors while reducing false positives or negatives.
- Battery Life: Many sniffing drones are still constrained by battery limitations, especially when using power-hungry sensors.
- Data Security: Given the sensitive nature of the data being collected (e.g., environmental pollution or chemical threats), ensuring the security of that data during transmission is crucial.
The future of sniffing drone technology is promising, with continued advancements in sensor technology, artificial intelligence, and drone autonomy. These developments will likely lead to more widespread use in industries such as agriculture, environmental monitoring, public safety, and security.
The Big News
The Sky Is Falling..
Sniffing drones, equipped with sensors for detecting gases, chemicals, and other environmental hazards, have been deployed across various industries, including agriculture, security, disaster response, environmental monitoring, and industrial inspection. Below is a detailed breakdown of the specific types and models of sniffing drones, the organizations that employ them, and relevant examples:
1. AeroVironment Quantix Recon
- Sensor Type: The Quantix Recon is a multi-sensor drone equipped with both visual and gas detection sensors.
- Primary Uses: It is primarily used for environmental monitoring, agricultural assessments, and security operations.
- Gas Detection: While the Quantix Recon is not fully specialized in sniffing for gases, it can be integrated with environmental sensors that detect specific chemical agents or airborne particulates.
- Employers:
- Agricultural Industry: Farmers use it to monitor crop health and detect environmental stressors, including potential pollutants in the air or soil.
- Public Safety and Environmental Agencies: It has been employed by governments and agencies for pollution tracking, hazardous material detection, and natural disaster monitoring.
- Example Use Case: AeroVironment’s Quantix Recon has been used by environmental monitoring companies to inspect large agricultural plots for pesticide drift or contamination.
2. Quantum Systems Trinity F90+
- Sensor Type: The Trinity F90+ is a long-range drone with the ability to carry a wide range of payloads, including gas detection sensors.
- Primary Uses: It is mainly used for agricultural and industrial inspections, particularly for monitoring air quality, detecting leaks, and surveying large-scale environments such as forests or industrial sites.
- Gas Detection: It can be fitted with sensors like electrochemical sensors, MOS (Metal-Oxide Semiconductor) sensors, or photoionization detectors (PID) for detecting gases such as methane, ammonia, and VOCs (volatile organic compounds).
- Employers:
- Agriculture: Large-scale farms and agricultural companies use the Trinity F90+ for detecting crop diseases (which emit specific gases) and assessing soil health.
- Oil and Gas Industry: The drone is also deployed in the oil and gas industry to detect gas leaks in pipelines or processing facilities.
- Example Use Case: Quantum Systems has partnered with environmental agencies and agricultural services to assess air quality and detect harmful emissions from industrial processes or nearby farms.
3. Flyability Elios 2
- Sensor Type: The Elios 2 is a confined-space inspection drone that can be equipped with gas sensors, such as carbon monoxide (CO), hydrogen sulfide (H2S), and other toxic gas detectors.
- Primary Uses: It is specifically used for inspecting confined or hazardous spaces (like tanks, silos, or factories) for dangerous gases.
- Gas Detection: The drone’s modular payload system allows it to carry gas detection sensors that can identify toxic chemicals and gases.
- Employers:
- Industrial Inspections: Industrial facilities such as refineries, chemical plants, and factories use the Elios 2 to conduct gas leak inspections in hard-to-reach or dangerous areas.
- Search and Rescue: In hazardous environments, this drone is used to help emergency teams detect harmful gases and ensure safe entry for human personnel.
- Example Use Case: Flyability’s Elios 2 has been used by companies like Shell and BP to inspect oil and gas installations, ensuring safety by detecting dangerous gas concentrations without putting personnel at risk.
4. DJI Matrice 300 RTK with Gas Detection Payload
- Sensor Type: The Matrice 300 RTK is a versatile industrial drone that can carry various payloads, including gas detection sensors.
- Primary Uses: It is employed in environmental monitoring, industrial inspection, and search and rescue operations.
- Gas Detection: The Matrice 300 can be equipped with advanced gas sensors, such as Electrochemical and PID sensors, capable of detecting gases like methane, hydrogen sulfide (H2S), and other hazardous substances.
- Employers:
- Oil and Gas Companies: It is widely used by oil and gas companies to detect leaks in pipelines, storage facilities, and processing plants.
- Environmental Agencies: Regulatory bodies and environmental monitoring agencies use it to track pollution, emissions, and air quality.
- Example Use Case: ExxonMobil uses the DJI Matrice 300 RTK for pipeline inspections and environmental monitoring to detect leaks in remote areas, where human access is difficult or unsafe.
5. Draganfly Command UAV
- Sensor Type: The Draganfly Command is a drone system used in public safety, environmental monitoring, and law enforcement. It can be equipped with a variety of sensors, including gas detectors.
- Primary Uses: It is commonly used for disaster response, law enforcement, and search and rescue missions.
- Gas Detection: With the right payload, it can be used to detect harmful chemicals, gases, and biological agents in areas affected by natural disasters or industrial accidents.
- Employers:
- Emergency Response Teams: Firefighters, police, and rescue operations use these drones for identifying hazardous materials or gases in disaster zones.
- Environmental and Research Agencies: They are also employed by agencies conducting environmental studies or monitoring toxic emissions.
- Example Use Case: Draganfly’s Command UAV has been used by first responders in wildfires, where it helps to monitor air quality and detect the presence of toxic gases such as carbon monoxide.
6. Percepto Sparrow
- Sensor Type: The Sparrow by Percepto is a fully autonomous industrial drone that can carry a variety of sensors, including gas detectors and thermal imaging cameras.
- Primary Uses: It is used primarily in industrial inspections (particularly in mining, power plants, and chemical facilities) to monitor air quality, detect gas leaks, and assess environmental conditions.
- Gas Detection: The Sparrow can be outfitted with MOS sensors and PID sensors for detecting gases like methane, sulfur dioxide, or hydrogen sulfide.
- Employers:
- Mining Companies: These drones are widely used in mining operations to detect dangerous gas leaks or air quality issues in underground mines.
- Chemical and Power Plants: They are also used in chemical and energy industries for hazardous material and gas leak detection in remote or hard-to-reach areas.
- Example Use Case: Rio Tinto, a mining giant, has deployed the Percepto Sparrow drones to monitor air quality in mining operations, ensuring the safety of workers and preventing gas-related accidents.
7. Teledyne FLIR SkyRanger R70
- Sensor Type: The SkyRanger R70 is an industrial-grade drone capable of carrying a range of payloads, including gas detection sensors and thermal cameras.
- Primary Uses: It is primarily used in energy and infrastructure inspections, environmental monitoring, and hazardous materials detection.
- Gas Detection: The R70 can be equipped with sensors for detecting a variety of toxic gases, including methane, carbon monoxide, and other industrial pollutants.
- Employers:
- Oil & Gas Industry: Companies use it for inspecting pipelines and refineries for leaks.
- Environmental Monitoring Firms: These drones are used by environmental agencies to monitor air quality in urban or industrial zones.
- Example Use Case: The SkyRanger R70 is employed by BP for remote inspections of oil rigs and pipeline systems, allowing early detection of methane leaks and other toxic emissions.
Summary of Common Employers:
- Oil & Gas Industry: Companies like ExxonMobil, BP, and Shell use sniffing drones for leak detection and environmental monitoring.
- Agriculture: Agricultural operations employ drones like the Trinity F90+ and Quantix Recon for crop monitoring and disease detection.
- Industrial Inspections: Drones such as the Flyability Elios 2 and Percepto Sparrow are used by chemical plants, power stations, and mining companies for safety checks.
- Public Safety & Disaster Response: Drones are increasingly used by emergency responders (e.g., firefighters, police, search and rescue teams) to monitor dangerous environments after natural disasters or accidents.
- Environmental Monitoring Agencies: Government bodies and environmental agencies employ drones for monitoring air quality, detecting pollutants, and assessing environmental damage.
These sniffing drones play a crucial role in detecting hazards, ensuring safety, and maintaining operational efficiency across a wide range of industries. Their integration of advanced sensors, AI, and autonomous flight capabilities makes them an invaluable tool for modern environmental and industrial monitoring.
Government Drone Projects and DARPA Involvement
Drone technology has become a critical part of various government programs globally, ranging from surveillance and reconnaissance to logistics and environmental monitoring. Among these, the U.S. Department of Defense (DoD) and DARPA (Defense Advanced Research Projects Agency) have been at the forefront of cutting-edge drone development. While the public purpose of these programs is often well-publicized, they also have shadow purposes—which are less discussed publicly but can have significant strategic, military, or intelligence implications.
General Purpose vs. “Shadow Purposes” of Government Drone Projects
1. General Purpose:
- Surveillance & Reconnaissance: Drones are primarily used by governments for intelligence gathering, border patrol, and surveillance of both domestic and international threats.
- Counter-Terrorism: Drones are employed in counterterrorism operations to track and neutralize threats, including targeted strikes using armed drones.
- Environmental Monitoring: Drones are deployed for monitoring environmental changes, such as pollution, climate change, and disaster management (e.g., wildfires, floods).
- Search and Rescue: Drones equipped with thermal imaging, sensors, and cameras are used in disaster zones to locate victims.
- Logistics & Delivery: Some government drone programs focus on using unmanned aerial systems (UAS) for delivering supplies to remote locations or during emergencies.
2. Shadow Purposes:
- Espionage & Surveillance: Governments often use drones to monitor foreign territories, track geopolitical rivals, or gather intelligence without risking human lives.
- Covert Operations: Drones can be used for covert military operations, such as surreptitious surveillance or intercepting communications in hostile territories.
- Psychological Operations (PsyOps): The use of drones for information warfare, such as disinformation campaigns or propaganda delivery, is also a possibility, though rarely confirmed.
- Cybersecurity and Hacking: Some drones are equipped with cyber capabilities to intercept communications, hack networks, or even disable enemy drones through electromagnetic pulses (EMP) or jamming techniques.
- Autonomous Weapons: Military drones, especially those under DARPA, are being explored as potential platforms for autonomous weapons that could target and eliminate threats without human intervention.
Key U.S. Government Drone Projects and DARPA Involvement
DARPA plays a crucial role in funding and advancing next-generation drone technology through various projects. Below are some notable government and DARPA-funded drone programs:
1. DARPA’s Gremlins Program
- Purpose: The Gremlins Program aims to develop a new class of low-cost, reusable drones that can be deployed and recovered from manned aircraft or other drones mid-flight. The goal is to reduce the cost of operating drone swarms and improve their flexibility in combat scenarios.
- Capabilities:
- Swarm Technology: Gremlins are designed to operate in swarms to overwhelm adversaries or conduct complex surveillance.
- Reusability: The drones can be launched, retrieved, and reused multiple times, which provides a significant reduction in operational costs.
- Shadow Purposes:
- Deployable on-demand: Gremlins could be used for surveillance or reconnaissance missions behind enemy lines, with minimal risk to expensive military assets.
- Asymmetric Warfare: These drones could be used for disrupting enemy operations, especially in regions with sophisticated anti-aircraft defenses.
2. DARPA’s ALIAS (Airborne Layers of Autonomous Systems) Program
- Purpose: The ALIAS Program is focused on making existing aircraft autonomous, with the goal of reducing the need for human pilots and enhancing the performance and safety of military operations.
- Capabilities:
- Autonomous Flight: ALIAS retrofits commercial or military aircraft with autonomous capabilities, which allow for flight without human input. It also includes advanced automated navigation systems and decision-making.
- Pilot Augmentation: In some cases, ALIAS is designed to assist human pilots by automating certain tasks or taking over in critical moments, such as in emergency landings.
- Shadow Purposes:
- Autonomous Combat Aircraft: A potential future iteration of ALIAS could turn manned aircraft into autonomous weapon systems, operated remotely or without human intervention, making decisions about targets and attack sequences.
- Psychological Warfare: ALIAS could be used for autonomous airstrikes with minimal traceability to human decision-makers, complicating the attribution of blame in covert military operations.
3. DARPA’s VAPR (Vortex Assisted Propulsion and Reconnaissance) Program
- Purpose: This program explores vortex-based propulsion to develop drones capable of flying in turbulent environments, such as urban warfare or harsh natural environments (e.g., dense forests or mountains).
- Capabilities:
- Vortex Propulsion: This system uses a unique approach to generate lift and thrust, allowing for vertical takeoff and landing (VTOL) in environments where traditional rotorcraft might struggle.
- Enhanced Maneuverability: VAPR drones can maneuver in tight spaces while carrying out surveillance, reconnaissance, or target acquisition missions.
- Shadow Purposes:
- Urban Warfare: These drones could be used in urban surveillance or to deploy covert biological or chemical agents in densely populated areas, where traditional drones cannot operate efficiently.
- Counter-Insurgency: VAPR could be used for operations in complex environments like underground tunnels or enemy-controlled urban zones.
4. DARPA’s Tactically Exploited Reconnaissance Node (TERN)
- Purpose: TERN seeks to create autonomous, long-range drones capable of launching and landing from smaller platforms, such as ships at sea.
- Capabilities:
- Autonomous Launch and Recovery: The drones are designed to be launched from and recovered by ships without the need for complex infrastructure.
- Long-Range Reconnaissance: TERN drones are capable of flying long distances to provide real-time intelligence, surveillance, and reconnaissance (ISR).
- Shadow Purposes:
- Secrecy and Denial: TERN drones could be used for covert maritime operations, including spying on enemy ships or even disabling enemy naval platforms with advanced payloads.
- Remote Warfare: These drones could act as “ghost ships”, providing surveillance and targeting data while remaining undetected or unreachable by enemy forces.
5. MQ-9 Reaper (U.S. Air Force)
- Purpose: The MQ-9 Reaper is a remotely piloted aircraft used primarily by the U.S. Air Force for surveillance, reconnaissance, and strike missions. It can carry a variety of payloads, including laser-guided bombs and missiles.
- Capabilities:
- Surveillance: Equipped with advanced sensors (e.g., synthetic aperture radar (SAR), infrared sensors, EO/IR cameras), it provides 24/7 surveillance over large areas.
- Strike Capability: The MQ-9 can carry precision-guided munitions to eliminate high-value targets.
- Shadow Purposes:
- Targeted Assassinations: The MQ-9 has been used for targeted killings of high-value individuals, a controversial aspect of modern warfare.
- Espionage: The Reaper can be used for spy missions in hostile territories without the need for human intelligence officers to be on the ground.
- Psychological Warfare: The constant surveillance of adversaries can act as a form of psychological pressure, knowing that a drone might be watching at any time.
6. U.S. Border Patrol Drones
- Purpose: Drones for border security have been deployed along the U.S. southern and northern borders to monitor illegal crossings, drug trafficking, and human smuggling.
- Capabilities:
- Surveillance: These drones are equipped with high-resolution cameras, thermal imaging, and infrared sensors to monitor large areas for unauthorized activity.
- Real-time Tracking: Drones can be used to track individuals or vehicles suspected of illegal activity across the border.
- Shadow Purposes:
- Targeting and Detention: Drones could potentially be used to identify targets for border patrol agents to intercept, sometimes without the suspects’ knowledge.
- Mass Surveillance: These systems contribute to the expansion of mass surveillance on citizens, which raises concerns about privacy rights and civil liberties.
Conclusion
Government drone projects—especially those spearheaded by DARPA—represent the cutting edge of technology and often straddle the line between transparent military and industrial applications and covert, sensitive operations. These projects serve not only obvious purposes like national security and disaster management but also have shadow purposes that involve espionage, cyber warfare, and the development of autonomous systems that could significantly alter military operations, covert activities, and global power dynamics. While the public focus is often on surveillance and environmental monitoring, many of these systems are being designed to support autonomous combat, covert strikes, and intelligence operations, thus playing a crucial role in modern asymmetric warfare and intelligence gathering.