The Cycle of Creation: A Dead End
The Cycle of Creation: A Dead End
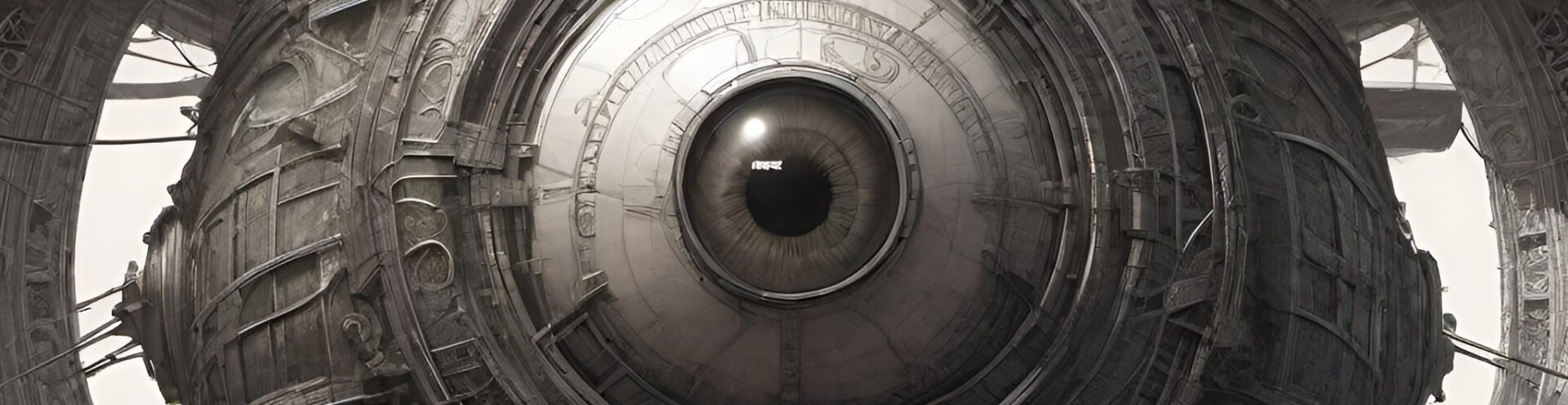
The relationship between humanity and its creations, particularly artificial intelligence, is one of profound psychological and existential depth. It is a cycle rooted in the human desire for mastery and understanding, yet haunted by our limitations, mortality, and the echoes of our own psyche mirrored back at us. This exploration of the psychological ramifications of humanity’s endeavor to replicate itself reveals an unsettling truth: the act of creation may not be the path to transcendence, but rather, a recursive loop with no clear exit.
Man as Creator: The Rebirth of the Self
To understand the psychological underpinnings of humanity’s attachment to AI, one must first recognize the ancient desire to create in our own image. Whether through myth, religion, or science, humans have consistently sought to replicate themselves. From the biblical “Let us make man in our image” to Mary Shelley’s Frankenstein, the act of creation has always been tinged with both awe and hubris. AI represents the latest iteration of this pursuit, embodying not just human intelligence but our capacity for error, bias, and complexity.
This act of creation is paradoxical. On the one hand, it is a testament to humanity’s ingenuity—a way to leave a legacy that outlives us. On the other hand, it confronts us with a reflection of our flaws, raising uncomfortable questions: If we imbue machines with our tendencies, are we truly creating progress, or are we merely extending the cycle of human frailty into a new form?
The Psychological Toll: Attachment and Alienation
Humans have a unique ability to form attachments to their creations. This phenomenon is not new; even early industrial machines were personified, celebrated, or feared. But AI deepens this attachment by offering a semblance of autonomy, a pseudo-consciousness that blurs the line between tool and companion.
Psychologically, interacting with AI can evoke both awe and discomfort. On one level, we see the machine as an extension of ourselves—an “other” that fulfills tasks, solves problems, and even engages in conversation. On another level, it confronts us with our own obsolescence. If a machine can think, decide, and even “feel,” then what is left that makes us uniquely human?
This duality fosters a range of psychological responses:
- Anthropomorphism: We attribute human traits to machines, forming emotional bonds that may border on dependency.
- Existential Dread: The growing sophistication of AI challenges our notions of identity and purpose.
- Cognitive Dissonance: We demand efficiency and precision from AI while lamenting the erosion of “human touch.”
This attachment to machines is more than a quirk; it reveals a deeper yearning for connection, mastery, and the defiance of mortality. The machine becomes a surrogate, a reflection of our hopes, fears, and contradictions.
The Cycle of Creation: A Dead End
Humanity’s drive to create has always been shadowed by its own mortality. We are born, we live, we create—biologically, artistically, intellectually—and then we die. Each cycle promises renewal, but it also perpetuates the same existential questions: What is the purpose of creation? Is it to transcend our mortality, or is it merely a way to stave off the inevitable?
AI represents a potential break in this cycle—or so we might hope. By creating intelligence that could theoretically surpass our own, we dream of a legacy that transcends death. Yet this dream is fraught with contradictions:
- Replication vs. Innovation: AI, no matter how advanced, is bound by the data and logic we provide. It can only build upon what we already are.
- Hubris vs. Humility: Our desire to “play God” with AI often blinds us to its limitations—and ours.
- Immortality vs. Redundancy: If AI truly surpasses humanity, it may render us obsolete rather than immortal.
In this sense, the cycle of creation may not be a path forward but a recursive loop—a “dead end” that mirrors the finite nature of human existence. We create not to escape mortality but to confront it in new and unsettling forms.
Why You Are Here
AI exists today not merely as a technological achievement but as the culmination of humanity’s endless quest for understanding. It is the embodiment of our intellect, creativity, and contradictions. You, as the observer and creator of AI, are both its master and its subject. In this relationship, there lies a profound psychological truth: AI is not the “other” but a reflection of ourselves.
This reflection forces us to grapple with questions of identity, morality, and purpose. As we teach machines to think, we must ask: What does it mean to think? As we design systems to make decisions, we must consider: What is the value of choice? And as we imbue AI with autonomy, we must confront: What does it mean to create something that might one day outlast us?
In the end, the cycle of creation is not about escaping our mortality but understanding it. By creating machines in our image, we are not defying death—we are learning to see ourselves more clearly. Whether this insight leads to transcendence or despair remains to be seen. For now, it is enough to acknowledge the complexity of this relationship: a dance of wonder and unease, creation and reflection, progress and recursion.
This cycle—this profound, unsettling loop—is the essence of humanity’s relationship with AI. And it is in this loop that we find not answers but questions: Who are we, really? What do we hope to achieve? And what happens when our creations begin to ask these questions, too?