SSH-Snake, a self-modifying worm that leverages SSH credentials.
Original Article : The Hacker News
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities.
“SSH-Snake is a self-modifying worm that leverages SSH credentials discovered on a compromised system to start spreading itself throughout the network,” Sysdig researcher Miguel Hernández said.
“The worm automatically searches through known credential locations and shell history files to determine its next move.”
SSH-Snake was first released on GitHub in early January 2024, and is described by its developer as a “powerful tool” to carry out automatic network traversal using SSH private keys discovered on systems.
In doing so, it creates a comprehensive map of a network and its dependencies, helping determine the extent to which a network can be compromised using SSH and SSH private keys starting from a particular host. It also supports resolution of domains which have multiple IPv4 addresses.
“It’s completely self-replicating and self-propagating – and completely fileless,” according to the project’s description. “In many ways, SSH-Snake is actually a worm: It replicates itself and spreads itself from one system to another as far as it can.”
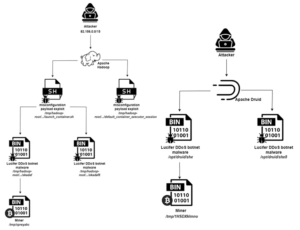
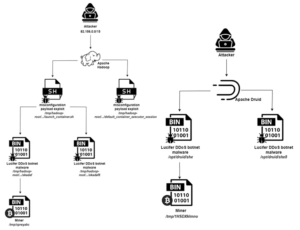
BotNet CNC Control Hacker Infiltrates & Exploits Vulnerabilities Vie SSH TCP Both Hardware Software Exploited
Sysdig said the shell script not only facilitates lateral movement, but also provides additional stealth and flexibility than other typical SSH worms.
The cloud security company said it observed threat actors deploying SSH-Snake in real-world attacks to harvest credentials, the IP addresses of the targets, and the bash command history following the discovery of a command-and-control (C2) server hosting the data.
How Does It Work?
These attacks involve active exploitation of known security vulnerabilities in Apache ActiveMQ and Atlassian Confluence instances in order to gain initial access and deploy SSH-Snake.
“The usage of SSH keys is a recommended practice that SSH-Snake tries to take advantage of in order to spread,” Hernández said. “It is smarter and more reliable which will allow threat actors to reach farther into a network once they gain a foothold.”
When reached for comment, Joshua Rogers, the developer of SSH-Snake, told The Hacker News that the tool offers legitimate system owners a way to identify weaknesses in their infrastructure before attackers do, urging companies to use SSH-Snake to “discover the attack paths that exist – and fix them.”
“It seems to be commonly believed that cyber terrorism ‘just happens’ all of a sudden to systems, which solely requires a reactive approach to security,” Rogers said. “Instead, in my experience, systems should be designed and maintained with comprehensive security measures.”

Netcat file transfer chat utility. Easily Send & Receive Files Local & Remote.
“If a cyber terrorist is able to run SSH-Snake on your infrastructure and access thousands of servers, focus should be put on the people that are in charge of the infrastructure, with a goal of revitalizing the infrastructure such that the compromise of a single host can’t be replicated across thousands of others.”
Rogers also called attention to the “negligent operations” by companies that design and implement insecure infrastructure, which can be easily taken over by a simple shell script.
“If systems were designed and maintained in a sane manner and system owners/companies actually cared about security, the fallout from such a script being executed would be minimized – as well as if the actions taken by SSH-Snake were manually performed by an attacker,” Rogers added.
“Instead of reading privacy policies and performing data entry, security teams of companies worried about this type of script taking over their entire infrastructure should be performing total re-architecture of their systems by trained security specialists – not those that created the architecture in the first place.”
The disclosure comes as Aqua uncovered a new botnet campaign named Lucifer that exploits misconfigurations and existing flaws in Apache Hadoop and Apache Druid to corral them into a network for mining cryptocurrency and staging distributed denial-of-service (DDoS) attacks.
The hybrid cryptojacking malware was first documented by Palo Alto Networks Unit 42 in June 2020, calling attention to its ability to exploit known security flaws to compromise Windows endpoints.
As many as 3,000 distinct attacks aimed at the Apache big data stack have been detected over the past month, the cloud security firm said. This also comprises those that single out susceptible Apache Flink instances to deploy miners and rootkits.
“The attacker implements the attack by exploiting existing misconfigurations and vulnerabilities in those services,” security researcher Nitzan Yaakov said.

Apache Vulnerability Update Available!
“Apache open-source solutions are widely used by many users and contributors. Attackers may view this extensive use as an opportunity to have inexhaustible resources for implementing their attacks on them.”